The best way to Clear Downloads – Protected, Easy, and Sensible Cleanup – Cyber Tech
Have you ever ever opened your Downloads folder and located hundreds of outdated recordsdata you didn’t even know existed? PDFs, installers, receipts, duplicate experiences — all quietly piling up.
Now think about these recordsdata sitting there for months or years. Amongst them may very well be delicate information, phishing attachments, and even malware that slipped previous your antivirus. For a cybersecurity skilled or government, that’s not muddle — that’s threat.
Studying the right way to clear downloads is not only about liberating disk house. It’s about defending your group’s techniques, bettering efficiency, and imposing sensible information hygiene throughout the digital workspace.
Let’s discover, in depth, the right way to clear your downloads safely and effectively — with out shedding essential information or breaking compliance.
Why It’s Essential to Clear Your Downloads
Your Downloads folder is a digital catch-all. Each browser, e mail shopper, and software program installer drops recordsdata there by default. Over time, it turns into a breeding floor for vulnerabilities.
1. Cybersecurity Dangers
Previous downloads typically include unverified or outdated recordsdata. A single malicious attachment — even one you by no means opened — may include dormant code ready to be triggered.
Attackers additionally exploit forgotten downloads to stage insider threats or lateral motion inside networks. For safety professionals, this can be a key information hygiene concern.
2. Privateness and Compliance
Many recordsdata within the Downloads folder might include confidential or personally identifiable info (PII): invoices, credentials, experiences, or contracts. Storing them indefinitely violates privateness rules corresponding to information minimization underneath GDPR or HIPAA.
3. System Efficiency
Massive Downloads folders decelerate indexing, backup, and antivirus scanning. When recordsdata pile up, system operations turn out to be sluggish — particularly on older or shared units.
4. Skilled Credibility
For executives and cybersecurity groups, a cluttered native surroundings displays poor operational self-discipline. Clear techniques undertaking accountability and take care of digital hygiene — important traits for any cybersecurity chief.
Frequent Secondary Key phrases
To make this content material complete and Search engine optimization-friendly, we’ll naturally embrace:
Understanding How Obtain Litter Builds Up
Earlier than diving into cleanup strategies, it’s helpful to know how the issue develops.
-
Browsers Robotically Save Information
Chrome, Edge, Firefox, and Safari all save downloads routinely — typically with out person affirmation. This default conduct encourages accumulation. -
A number of Units and Accounts
Syncing accounts throughout work and private techniques multiplies duplicates. Your recordsdata might exist in a number of folders on completely different units. -
Momentary File Habits
Installers (.exe, .pkg, .zip) or experiences are sometimes one-time-use however by no means deleted manually afterward. -
Human Habits
Individuals not often revisit their downloads. The “I’ll manage this later” mindset results in months of buildup.
When you acknowledge how muddle grows, it turns into clear why common cleanup should be a part of your cybersecurity routine.
The best way to Clear Downloads Safely (Step-by-Step)
Let’s break this course of into 5 professional-grade steps you’ll be able to apply to private techniques, enterprise machines, or managed networks.
Step 1: Evaluate and Categorize Information
Earlier than you delete something, analyze what’s in your Downloads folder.
-
Kind by Date: Begin with the oldest recordsdata — most are not wanted.
-
Kind by Sort: Establish installers (.exe, .dmg, .zip), paperwork (.pdf, .docx), and media (.jpg, .mp4).
-
Search by Key phrase: Search for delicate file names (e.g., “password,” “bill,” “contract”).
Professional Tip: Cybersecurity groups ought to use PowerShell or Bash instructions to export file metadata (dimension, sort, creation date) earlier than deletion — best for auditing or compliance logs.
Step 2: Transfer Essential Information Elsewhere
Don’t delete all the pieces directly. As a substitute, transfer what issues.
-
Create an “Archive” folder: Switch project-related or business-critical downloads into this folder.
-
Retailer securely: Transfer delicate recordsdata to encrypted drives or cloud repositories with entry management.
-
Rename for readability: Use constant naming conventions earlier than archiving — e.g., “ClientReport_Q1_2026.pdf”.
⚙️ Should you’re managing a number of customers, configure automated backups utilizing OneDrive, Dropbox, or enterprise-grade cloud sync instruments.
Step 3: Delete Pointless Information
Now comes the cleanup.
Guide Technique (for Private Use)
-
On Home windows:
Open Downloads → Ctrl+A → Delete.
Then empty your Recycle Bin. -
On macOS:
Finder → Downloads → Command+A → Transfer to Trash → Empty Trash. -
On Linux:
Open Terminal and use:(Warning: irreversible.)
Automated Technique (for Groups or Servers)
Use automation scripts or insurance policies:
-
Home windows PowerShell:
-
macOS/Linux Cron Jobs:
Professional Tip: Maintain a 30-day retention coverage — delete recordsdata older than 30 days except marked “don’t take away.”
Step 4: Empty Browser Obtain Histories
Even after deleting recordsdata, browsers retain obtain logs that expose delicate metadata.
For Google Chrome
-
Open Chrome.
-
Press
Ctrl+J(Home windows) orCmd+J(Mac). -
Click on “Clear all.”
For Microsoft Edge
-
Go to Settings → Downloads.
-
Click on Clear Obtain Historical past.
For Firefox & Safari
Use Library → Historical past → Clear Latest Historical past.
Eradicating this information prevents others from reconstructing your exercise — a key privateness layer for executives and analysts.
Step 5: Set Up Computerized Cleanup Insurance policies
Guide cleansing is reactive. Sensible leaders make it automated.
-
Group Coverage Objects (GPOs): Configure company Home windows environments to clear downloads at login/logout.
-
Endpoint Administration Platforms: Use instruments like Microsoft Intune, Jamf, or CrowdStrike to implement insurance policies and monitor storage.
-
Browser Controls: Pressure browsers to ask for obtain places fairly than defaulting to at least one folder.
Automation reduces human error and standardizes digital hygiene throughout the corporate.
The best way to Clear Downloads on Totally different Units
Cybersecurity professionals typically handle hybrid fleets — Home windows, macOS, cell, or digital machines. Right here’s a fast rundown:
Home windows 10/11
macOS
Android
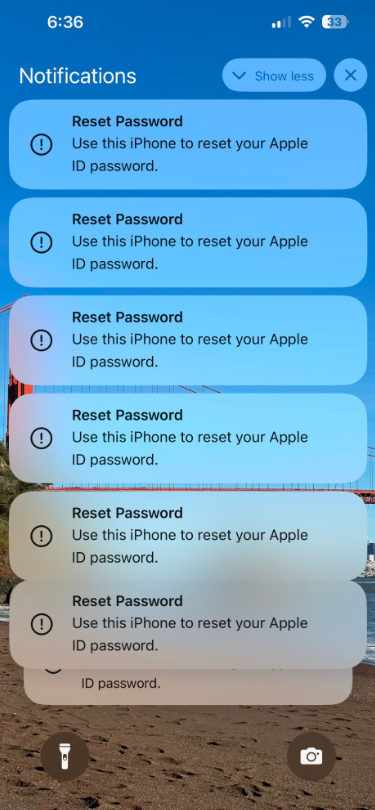
iPhone/iPad
Integrating Obtain Cleanup into Safety Coverage
For leaders managing digital environments, “the right way to clear downloads” ought to evolve right into a policy-driven routine, not a one-time activity.
1. Outline Retention Thresholds
Set up a uniform customary:
“All downloads older than 30 days are routinely deleted except explicitly archived.”
2. Classify Obtain Varieties
Categorize recordsdata as non permanent, everlasting, or restricted.
Use Information Loss Prevention (DLP) instruments to tag delicate content material.
3. Limit Entry and Permissions
Restrict write entry to Downloads folders on shared techniques.
Redirect downloads to sandboxed drives or safe community shares.
4. Monitor and Report
Use analytics instruments to trace:
These metrics will be built-in into broader cybersecurity KPIs.
Finest Practices to Maintain Downloads Clear and Safe
-
Evaluate weekly: Add a calendar reminder.
-
Keep away from saving passwords or invoices in Downloads.
-
Allow browser prompts: At all times select the place to avoid wasting recordsdata.
-
Use encryption for delicate recordsdata earlier than obtain.
-
Apply antivirus scanning on each new file.
-
Educate workers: Embody obtain hygiene in cybersecurity consciousness coaching.
Frequent Errors to Keep away from When Clearing Downloads
-
Deleting Every part With out Evaluate: You threat shedding necessary data or experiences.
-
Skipping Browser Historical past Cleanup: Information could also be gone, however logs nonetheless reveal what was downloaded.
-
Neglecting Shared or Cloud Folders: Some browsers redirect downloads to synced places like OneDrive or Google Drive.
-
No Backup Technique: Deletion with out archiving breaks compliance for audit trails.
-
Ignoring Cellular Units: Many threats now originate from smartphone downloads.
Instruments for Smarter Obtain Administration
-
BleachBit: Open-source cleaner for safe file elimination.
-
CCleaner: Automates file cleanup and browser log deletion.
-
Microsoft Storage Sense: Constructed-in automation for Home windows techniques.
-
CleanMyMac X: Maintains macOS efficiency by clearing cache and downloads.
-
Enterprise Endpoint Instruments: CrowdStrike, Intune, or SentinelOne for coverage enforcement.
Select options that stability pace, security, and auditability.
Lengthy-Time period Digital Hygiene Technique
Cleansing downloads isn’t only a activity — it’s a part of your safety tradition.
Combine these long-term habits:
-
Quarterly Cleanups: Schedule digital “spring cleans” for all departments.
-
Consciousness Campaigns: Remind workers how outdated downloads can turn out to be safety liabilities.
-
Automated Retention Logs: Maintain audit trails for all deletions.
-
Position-Primarily based Insurance policies: Builders may have longer retention; executives may have stricter deletion.
By embedding obtain cleanup into firm tradition, you strengthen your group’s general resilience.
Conclusion: Sensible Cleanup Is Sensible Safety
Understanding the right way to clear downloads could appear easy — but it surely’s foundational to cybersecurity hygiene. Forgotten recordsdata can maintain malware, information leaks, and authorized threat.
For IT professionals and executives, common cleanup displays management in threat discount, efficiency optimization, and compliance excellence.
Take motion at the moment:
A couple of minutes of proactive cleanup can stop hours of harm management later. Digital security begins with habits — and your Downloads folder is the right place to begin.
FAQ: The best way to Clear Downloads
1. Why ought to I clear my Downloads folder frequently?
As a result of it reduces muddle, prevents information publicity, and eliminates hidden malware or phishing payloads.
2. Does deleting recordsdata from Downloads unlock house instantly?
Sure, however you need to additionally empty your Recycle Bin or Trash to reclaim storage fully.
3. Can I recuperate unintentionally deleted downloads?
Should you haven’t emptied the Recycle Bin or Trash, sure. In any other case, use restoration software program like Recuva or Time Machine backups.
4. Is it secure to delete all recordsdata in Downloads?
Sure — in the event that they’re backed up or not wanted. At all times confirm earlier than deleting work-related recordsdata.
5. How typically ought to I clear my Downloads folder?
At the very least as soon as a month; weekly for cybersecurity or IT-intensive roles.
6. What’s the perfect device to clear downloads safely?
For people, use built-in OS instruments like Disk Cleanup or Finder. For enterprises, automate via PowerShell, Intune, or customized scripts.
7. Can malware conceal within the Downloads folder?
Completely. Malicious recordsdata typically disguise themselves as innocent paperwork or updates. Common cleanup reduces threat publicity.
8. How do I train my workforce about obtain hygiene?
Embody it in cybersecurity coaching, ship periodic reminders, and create insurance policies that auto-delete outdated downloads.
✅ Closing Takeaway
A cluttered Downloads folder is greater than an inconvenience — it’s a safety legal responsibility.
Understanding the right way to clear downloads empowers professionals and organizations to keep up efficiency, defend delicate information, and domesticate a security-first mindset.
Begin now. Clear at the moment. Keep safe tomorrow.