BeatBanker and BTMOB trojans: an infection methods and how you can keep protected – Cyber Tech
To realize their malign goals, Android malware builders have to handle a number of challenges in a row: trick customers to get inside their smartphones, dodge safety software program, discuss victims into granting numerous system permissions, steer clear of built-in battery optimizers that kill useful resource hogs, and, in spite of everything that, be sure that their malware really turns a revenue. The creators of the BeatBanker — an Android‑primarily based malware marketing campaign not too long ago found by our consultants — have give you one thing new for every one among these steps. The assault is (for now) geared toward Brazilian customers, however the builders’ ambitions will nearly definitely push them towards worldwide enlargement, so it’s value staying on guard and finding out the risk actor’s methods. You could find a full technical evaluation of the malware on Securelist.
How BeatBanker infiltrates a smartphone
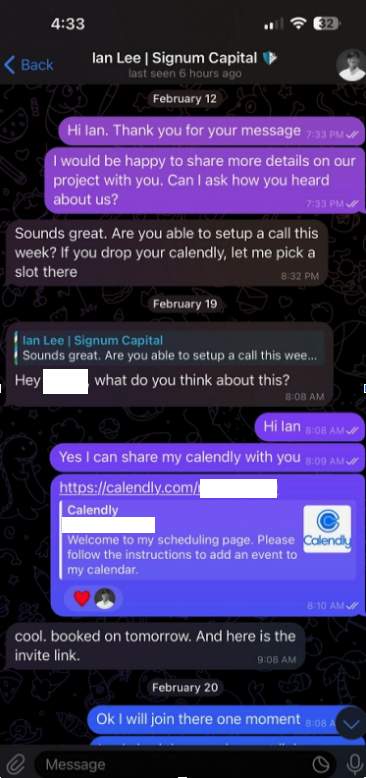
The malware is distributed via specifically crafted phishing pages that mimic the Google Play Retailer. A web page that’s simply mistaken for the official app market invitations customers to obtain a seemingly helpful app. In a single marketing campaign, the trojan disguised itself because the Brazilian authorities companies app, INSS Reembolso; in one other, it posed because the Starlink app.
The malicious web site cupomgratisfood{.}store does a superb job imitating an app retailer. It’s simply unclear why the faux INSS Reembolso seems all of thrice. To be further positive, maybe?!
The set up takes place in a number of phases to keep away from requesting too many permissions directly and to additional lull the sufferer’s vigilance. After the primary app is downloaded and launched, it shows an interface that additionally resembles Google Play and simulates an replace for the decoy app — requesting the consumer’s permission to put in apps, which doesn’t look out-of-the-ordinary in context. For those who grant this permission, the malware downloads extra malicious modules to your smartphone.
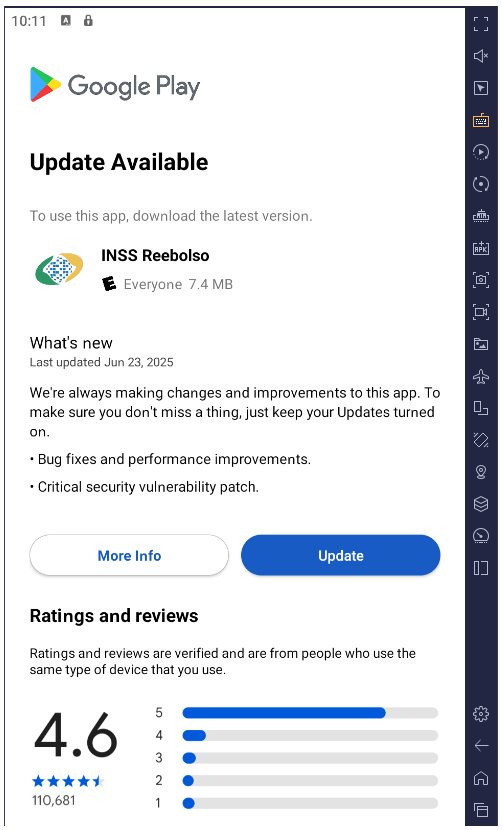
After set up, the trojan simulates a decoy app replace through Google Play by requesting permission to put in functions whereas downloading extra malicious modules within the course of
All elements of the trojan are encrypted. Earlier than decrypting and continuing to the following phases of an infection, it checks to make sure it’s on an actual smartphone and within the goal nation. BeatBanker instantly terminates its personal course of if it finds any discrepancies or detects that it’s working in emulated or evaluation environments. This complicates dynamic evaluation of the malware. By the way, the faux replace downloader injects modules instantly into RAM to keep away from creating recordsdata on the smartphone that might be seen to safety software program.
All these methods are nothing new and often utilized in advanced malware for desktop computer systems. Nonetheless, for smartphones, such sophistication continues to be a rarity, and never each safety instrument will spot it. Customers of Kaspersky merchandise are shielded from this risk.
Taking part in audio as a defend
As soon as established on the smartphone, BeatBanker downloads a module for mining Monero cryptocurrency. The authors had been very involved that the smartphone’s aggressive battery optimization programs would possibly shut down the miner, in order that they got here up with a trick: taking part in an all-but-inaudible sound always. Energy consumption management programs usually spare apps which might be taking part in audio or video to keep away from chopping off background music or podcast gamers. On this manner, the malware can run constantly. Moreover, it shows a persistent notification within the standing bar, asking the consumer to maintain the telephone on for a system replace.
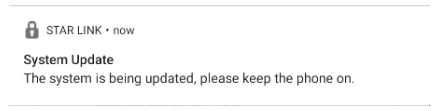
Instance of a persistent system replace notification from one other malicious app masquerading because the Starlink app
Management through Google
To handle the trojan, the authors leverage Google’s professional Firebase Cloud Messaging (FCM) — a system for receiving notifications and sending information from a smartphone. This function is offered to all apps and it’s the preferred technique for sending and receiving information. Because of FCM, attackers can monitor the system’s standing and alter its settings as wanted.
Nothing dangerous occurs for some time after the malware is put in: the attackers wait it out. Then they set off the miner, however they’re cautious to throttle it again if the telephone overheats, the battery begins dipping, or the proprietor occurs to be utilizing the system. All of that is dealt with through FCM.
Theft and espionage
Along with the crypto miner, BeatBanker installs further modules to spy on the consumer and rob them on the proper second. The spy ware module requests Accessibility Providers permission, and if that is granted, begins monitoring all the things that’s taking place on the smartphone.
If the proprietor opens the Binance or Belief Pockets app to ship USDT, the malware overlays a faux display on high of the pockets interface, successfully swapping the recipient’s deal with for its personal. All transfers go to the attackers.
The trojan options a complicated distant management system and is able to executing many different instructions:
- Intercepting one-time codes from Google Authenticator
- Recording audio from the microphone
- Streaming the display in real-time
- Monitoring the clipboard and intercept keystrokes
- Sending SMS messages
- Simulating faucets on particular areas of the display and textual content enter in line with a script despatched by the attacker, and far more
All of this makes it potential to rob the sufferer after they use every other banking or fee companies — not simply crypto funds.
Generally victims are contaminated with a special module for espionage and distant smartphone management — the BTMOB distant entry trojan. Its malicious capabilities are even broader, together with:
- Computerized acquisition of sure permissions on Android 13–15
- Steady geolocation monitoring
- Entry to the entrance and rear cameras
- Acquiring PIN codes and passwords for display unlocking
- Capturing keyboard enter
defend your self from BeatBanker
Cybercriminals are continually refining their assaults and developing with new methods to revenue from their victims. Regardless of this, you may defend your self by following just a few easy precautions:
- Obtain apps from official sources solely, akin to Google Play or the app retailer preinstalled by the seller. For those who discover an app whereas looking the web, don’t open it through a hyperlink out of your browser; as a substitute, head to the Google Play app or one other branded retailer in your smartphone to seek for it there. Whilst you’re at it, examine the variety of downloads, the app’s age, and take a look at the rankings and evaluations. Keep away from new apps, apps with low rankings, and people with a small variety of downloads.
- Verify any permissions you grant. Don’t grant permissions when you’re undecided what they do or why that particular app requires them. Be further cautious with permissions like Set up unknown apps, Accessibility, Superuser, and Show over different apps. We’ve written about these intimately in a separate article.
- Equip your system with a complete anti-malware resolution. We, naturally, suggest Kaspersky for Android. Customers of Kaspersky merchandise are shielded from BeatBanker — detected with the verdicts HEUR:Trojan-Dropper.AndroidOS.BeatBanker and HEUR:Trojan-Dropper.AndroidOS.Banker.*.
- Frequently replace each your working system and safety software program. For Kaspersky for Android, which is at present unavailable on Google Play, please assessment our detailed directions on putting in and updating the app.
Threats to Android customers have been going via the roof recently. Take a look at our different posts on essentially the most related and widespread Android assaults and ideas for conserving you and your family members protected: