What a browser-in-the-browser assault is, and the right way to spot a pretend login window – Cyber Tech
In 2022, we dived deep into an assault technique known as browser-in-the-browser — initially developed by the cybersecurity researcher referred to as mr.d0x. Again then, no precise examples existed of this mannequin getting used within the wild. Quick-forward 4 years, and browser-in-the-browser assaults have graduated from the theoretical to the actual: attackers at the moment are utilizing them within the area. On this put up, we revisit what precisely a browser-in-the-browser assault is, present how hackers are deploying it, and, most significantly, clarify the right way to hold your self from turning into its subsequent sufferer.
What’s a browser-in-the-browser (BitB) assault?
For starters, let’s refresh our reminiscences on what mr.d0x really cooked up. The core of the assault stems from his statement of simply how superior fashionable net growth instruments — HTML, CSS, JavaScript, and the like — have develop into. It’s this realization that impressed the researcher to give you a very elaborate phishing mannequin.
A browser-in-the-browser assault is a complicated type of phishing that makes use of net design to craft fraudulent web sites imitating login home windows for well-known companies like Microsoft, Google, Fb, or Apple that look similar to the actual factor. The researcher’s idea includes an attacker constructing a legitimate-looking web site to lure in victims. As soon as there, customers can’t depart feedback or make purchases except they “check in” first.
Signing in appears simple sufficient: simply click on the Check in with {fashionable service title} button. And that is the place issues get attention-grabbing: as a substitute of a real authentication web page supplied by the professional service, the consumer will get a pretend type rendered contained in the malicious web site, wanting precisely like… a browser pop-up. Moreover, the tackle bar within the pop-up, additionally rendered by the attackers, shows a completely professional URL. Even an in depth inspection received’t reveal the trick.
From there, the unsuspecting consumer enters their credentials for Microsoft, Google, Fb, or Apple into this rendered window, and people particulars go straight to the cybercriminals. For some time this scheme remained a theoretical experiment by the safety researcher. Now — real-world attackers have added it to their arsenals.
Fb credential theft
Attackers have put their very own spin on mr.d0x’s authentic idea: current browser-in-the-browser hits have been kicking off with emails designed to alarm recipients. As an example, one phishing marketing campaign posed as a regulation agency informing the consumer they’d dedicated a copyright violation by posting one thing on Fb. The message included a credible-looking hyperlink allegedly to the offending put up.
Attackers despatched messages on behalf of a pretend regulation agency alleging copyright infringement — full with a hyperlink supposedly to the problematic Fb put up. Supply
Curiously, to decrease the sufferer’s guard, clicking the hyperlink didn’t instantly open a pretend Fb login web page. As an alternative, they have been first greeted by a bogus Meta CAPTCHA. Solely after passing it was the sufferer introduced with the pretend authentication pop-up.
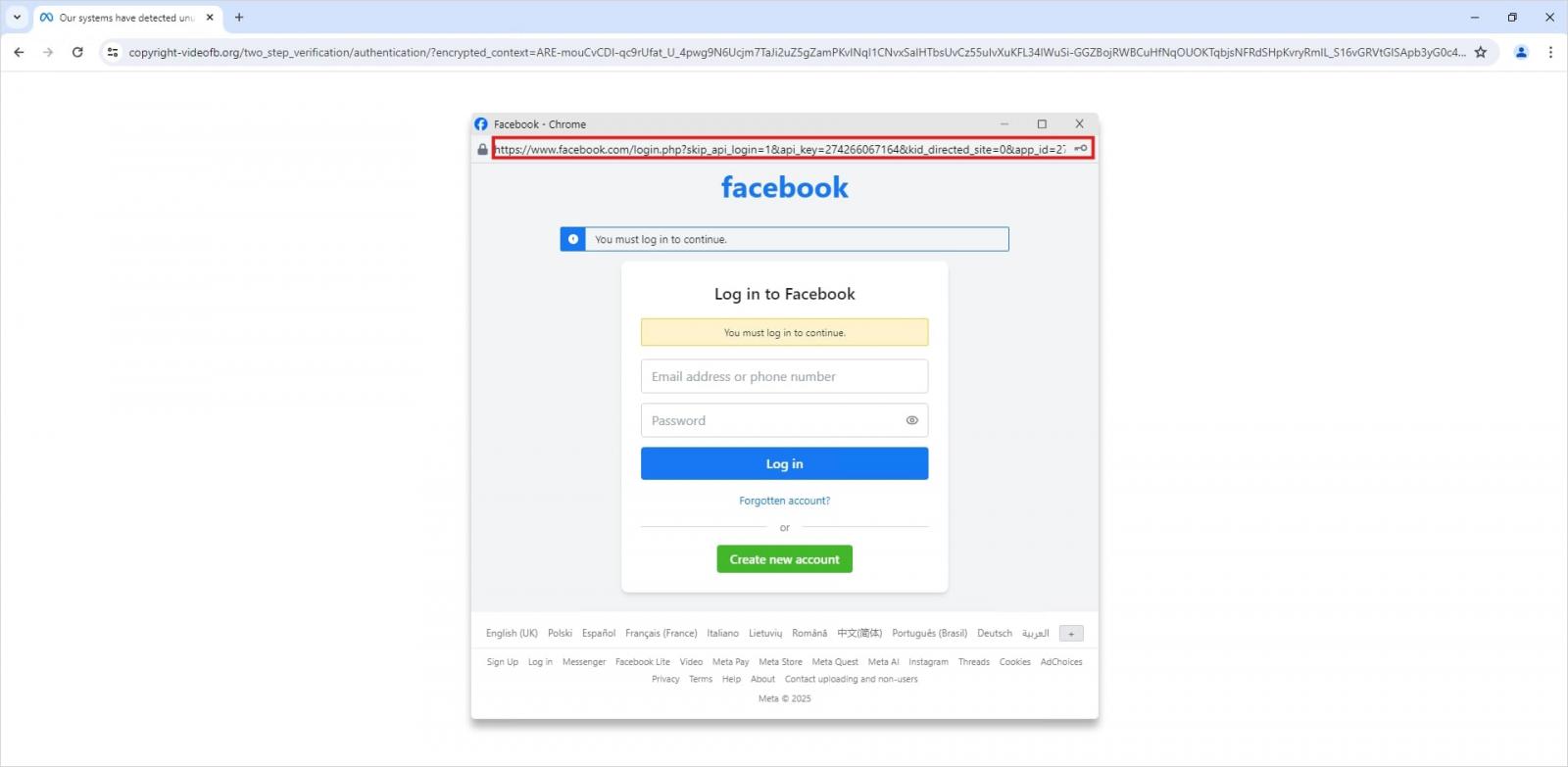
This isn’t an actual browser pop-up; it’s an internet site component mimicking a Fb login web page — a ruse that enables attackers to show a wonderfully convincing tackle. Supply
Naturally, the pretend Fb login web page adopted mr.d0x’s blueprint: it was constructed totally with net design instruments to reap the sufferer’s credentials. In the meantime, the URL displayed within the cast tackle bar pointed to the actual Fb web site — www.fb.com.
The way to keep away from turning into a sufferer
The truth that scammers at the moment are deploying browser-in-the-browser assaults simply goes to point out that their bag of methods is consistently evolving. However don’t despair — there’s a method to inform if a login window is legit. A password supervisor is your good friend right here, which, amongst different issues, acts as a dependable safety litmus take a look at for any web site.
That’s as a result of relating to auto-filling credentials, a password supervisor appears to be like on the precise URL, not what the tackle bar seems to point out, or what the web page itself appears to be like like. In contrast to a human consumer, a password supervisor can’t be fooled with browser-in-the-browser techniques, or another methods, like domains having a barely totally different tackle (typosquatting) or phishing types buried in adverts and pop-ups. There’s a easy rule: in case your password supervisor affords to auto-fill your login and password, you’re on an internet site you’ve beforehand saved credentials for. If it stays silent, one thing’s fishy.
Past that, following our time-tested recommendation will make it easier to defend in opposition to varied phishing strategies, or no less than decrease the fallout if an assault succeeds:
- Allow two-factor authentication (2FA) for each account that helps it. Ideally, use one-time codes generated by a devoted authenticator app as your second issue. This helps you dodge phishing schemes designed to intercept affirmation codes despatched by way of SMS, messaging apps, or e-mail. You may learn extra about one-time-code 2FA in our devoted put up.
- Use passkeys. The choice to check in with this technique may also function a sign that you just’re on a professional web site. You may be taught all about what passkeys are and the right way to begin utilizing them in our deep dive into the expertise.
- Set distinctive, advanced passwords for all of your accounts. No matter you do, by no means reuse the identical password throughout totally different accounts. We lately lined what makes a password really robust on our weblog. To generate distinctive combos — without having to recollect them — Kaspersky Password Supervisor is your greatest wager. As an added bonus, it could additionally generate one-time codes for two-factor authentication, retailer your passkeys, and synchronize your passwords and information throughout your varied units.
Lastly, this put up serves as yet one more reminder that theoretical assaults described by cybersecurity researchers typically discover their manner out into the wild. So, keep watch over our weblog, and subscribe to our Telegram channel to remain in control on the newest threats to your digital safety and the right way to shut them down.
Examine different ingenious phishing methods scammers are utilizing day in day trip: