Native KTAE and the IDA Professional plugin – Cyber Tech
In a earlier put up, we walked by a sensible instance of how risk attribution helps in incident investigations. We additionally launched the Kaspersky Risk Attribution Engine (KTAE) — our instrument for making an informed guess about which particular APT group a malware pattern belongs to. To exhibit it, we used the Kaspersky Risk Intelligence Portal — a cloud-based instrument that gives entry to KTAE as a part of our complete Risk Evaluation service, alongside a sandbox and a non-attributing similarity-search instrument. The benefits of a cloud service are apparent: purchasers don’t must put money into {hardware}, set up something, or handle any software program. Nonetheless, as real-world expertise reveals, the cloud model of an attribution instrument isn’t for everybody…
First, some organizations are certain by regulatory restrictions that strictly forbid any knowledge from leaving their inside perimeter. For the safety analysts at these companies, importing information to a third-party service is out of the query. Second, some firms make use of hardcore risk hunters who want a extra versatile toolkit — one which lets them work with their very own proprietary analysis alongside Kaspersky’s risk intelligence. That’s why KTAE is accessible in two flavors: a cloud-based model and an on-prem deployment.
What are the on-prem KTAE benefits over the cloud model?
First off, the native model of KTAE ensures an investigation stays absolutely confidential. All of the evaluation takes place proper within the group’s inside community. The risk intelligence supply is a database deployed inside the corporate perimeter; it’s full of the distinctive indicators and attribution knowledge of each malicious pattern recognized to our consultants; and it additionally comprises the traits pertaining to official information to exclude false-positive detections. The database will get common updates, however it operates one-way: no info ever leaves the shopper’s community.
Moreover, the on-prem model of KTAE provides consultants the flexibility so as to add new risk teams to the database and hyperlink them to malware samples they found on their very own. Which means subsequent attribution of recent information will account for the information added by inside researchers. This enables consultants to catalog their very own distinctive malware clusters, work with them, and establish similarities.
Right here’s one other useful professional instrument: our workforce has developed a free plugin for IDA Professional, a preferred disassembler, to be used with the native model of KTAE.
What’s the aim of an attribution plugin for a disassembler?
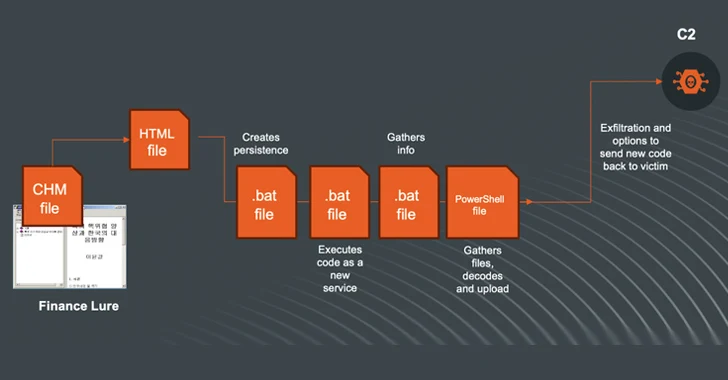
For a SOC analyst on alert triage, attributing a malicious file discovered within the infrastructure is easy: simply add it to KTAE (cloud or on-prem) and get a verdict, like Manuscrypt (83%). That’s enough for taking enough countermeasures towards that group’s recognized toolkit and assessing the general scenario. A risk hunter, nonetheless, won’t wish to take that verdict at face worth. Alternatively, they could ask, “Which code fragments are distinctive throughout all of the malware samples utilized by this group?” Right here an attribution plugin for a disassembler turns out to be useful.
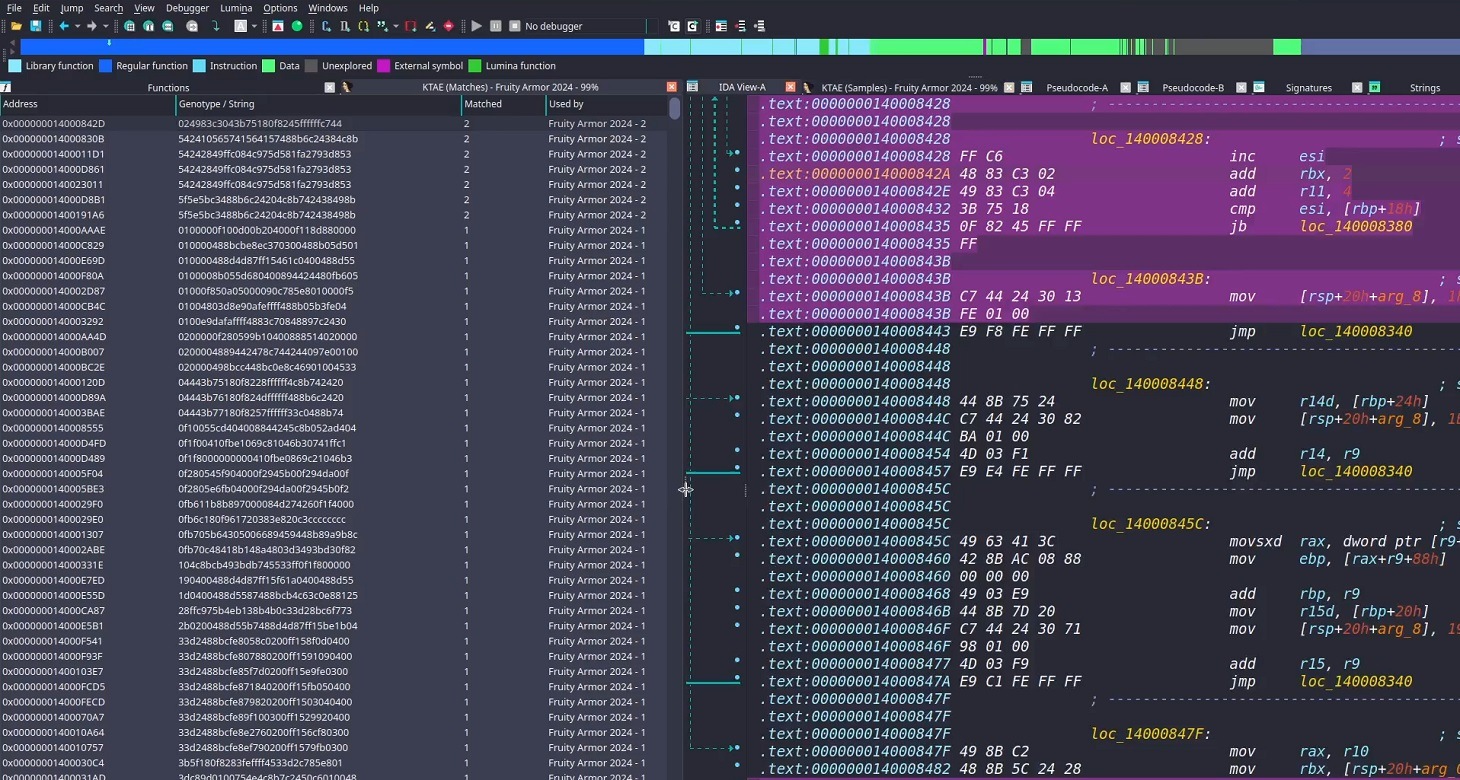
Contained in the IDA Professional interface, the plugin highlights the particular disassembled code fragments that triggered the attribution algorithm. This doesn’t simply permit for a extra expert-level deep dive into new malware samples; it additionally lets researchers refine attribution guidelines on the fly. Because of this, the algorithm — and KTAE itself — retains evolving, making attribution extra correct with each run.
How one can arrange the plugin
The plugin is a script written in Python. To get it up and working you want IDA Professional. Sadly, it gained’t work in IDA Free, because it lacks help for Python plugins. When you don’t have Python put in but, you’d must seize that, arrange the dependencies (verify the necessities file in our GitHub repository), and ensure IDA Professional surroundings variables are pointing to the Python libraries.
Subsequent, you’d must insert the URL on your native KTAE occasion into the script physique and supply your API token (which is accessible on a industrial foundation) — similar to it’s executed within the instance script described within the KTAE documentation.
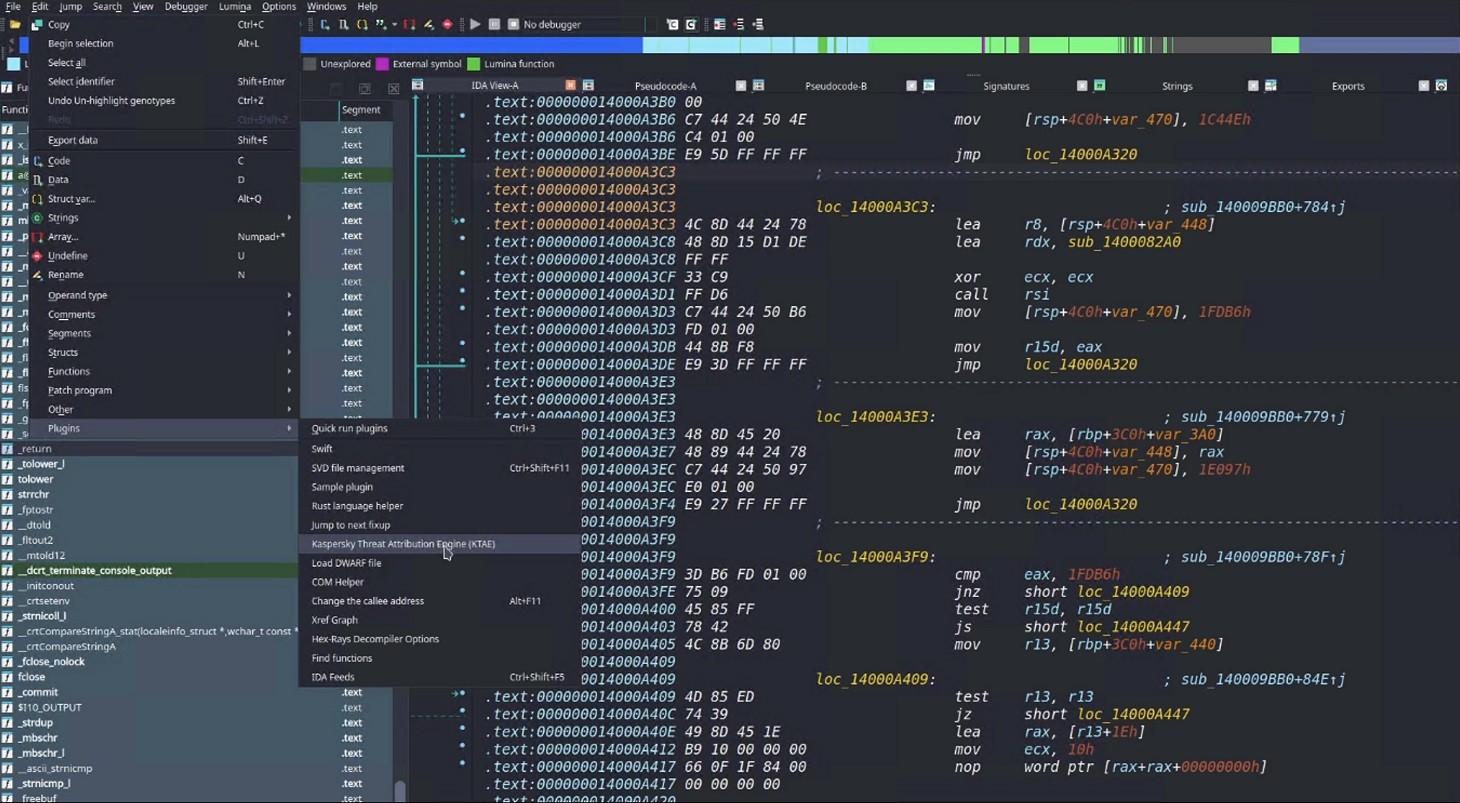
Then you’ll be able to merely drop the script into your IDA Professional plugins folder and hearth up the disassembler. When you’ve executed it proper, then, after loading and disassembling a pattern, you’ll see the choice to launch the Kaspersky Risk Attribution Engine (KTAE) plugin underneath Edit → Plugins:
How one can use the plugin
When the plugin is put in, right here’s what occurs underneath the hood: the file at present loaded in IDA Professional is shipped through API to the regionally put in KTAE service, on the URL configured within the script. The service analyzes the file, and the evaluation outcomes are piped proper again into IDA Professional.
On an area community, the script often finishes its job in a matter of seconds (the period is dependent upon the connection to the KTAE server and the dimensions of the analyzed file). As soon as the plugin wraps up, a researcher can begin digging into the highlighted code fragments. A double-click leads straight to the related part within the meeting or binary code (Hex view) for evaluation. These additional knowledge factors make it straightforward to identify shared code blocks and observe modifications in a malware toolkit.
To be taught extra in regards to the Kaspersky Risk Attribution Engine and how one can deploy it, take a look at the official product documentation. And to rearrange an indication or piloting undertaking, please fill out the shape on the Kaspersky web site.