Why Does Have I Been Pwned Comprise “Pretend” Electronic mail Addresses? – Cyber Tech
Usually, when somebody sends suggestions like this, I ignore it, but it surely occurs usually sufficient that it deserves an explainer, as a result of the reply is de facto, actually easy. So easy, in actual fact, that it ought to be evident to the likes of Bruce, who determined his misunderstanding deserved a 1-star Trustpilot assessment yesterday:
Now, frankly, Trustpilot is a reasonably questionable supply of real-world, high quality evaluations anyway, however the identical suggestions has come by way of different channels sufficient instances that permit’s simply kind this out as soon as and for all. All of it begins with one easy query:
What’s an Electronic mail Tackle?
You suppose you understand – and Bruce thinks he is aware of – however you may each be mistaken. To elucidate the reply to the query, we have to begin with how HIBP ingests knowledge, and that basically is fairly easy: somebody sends us a breach (which is usually simply textual content information of information), and we run the open supply Electronic mail Tackle Extractor instrument over it, which then dumps all of the distinctive addresses right into a file. That file is then uploaded into the system, the place the addresses are then searchable.
The logic for a way we extract addresses is all in that Github repository, however in easy phrases, it boils right down to this:
- There should be an @ image
- There will be as much as 64 characters earlier than it (the alias)
- There will be as much as 255 characters after it (the area)
- The area should include a interval
- The area should even have a sound TLD
- A number of different little standards which are all documented within the public repo
That’s all! We will not then inform if there’s an precise mailbox behind the handle, as that may require large per-address processing, for instance, sending an e-mail to every one and seeing if it bounces. Are you able to think about doing that 7 billion instances?! That is the variety of distinctive addresses in HIBP, and clearly, it is unattainable. So, meaning all the next have been parsed as being legitimate and loaded into HIBP (deep hyperlinks to the search consequence):
- take a look at@instance.com
- _test@google.com
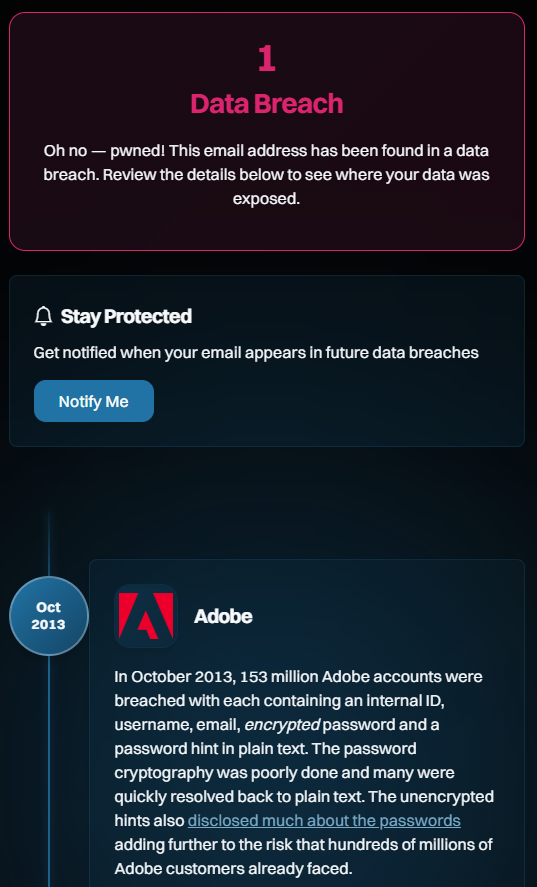
- fuckingwasteoftime@foo.com
I notably like that final one, because it appears like a sentiment Bruce would specific. It is also an awesome instance because it’s clearly not “actual”; the alias is a little bit of a giveaway, as is the area (“foo” is usually used as a placeholder, just like how we’d additionally use “bar”, or mix them as “foo bar”). However in the event you observe the hyperlink and see the breach it was uncovered in, you will see a really acquainted identify:
Which brings us to the subsequent query:
How Do “Pretend” Electronic mail Addresses Find yourself in Actual Web sites?
That is additionally going to look profoundly easy if you see it. Right here goes:
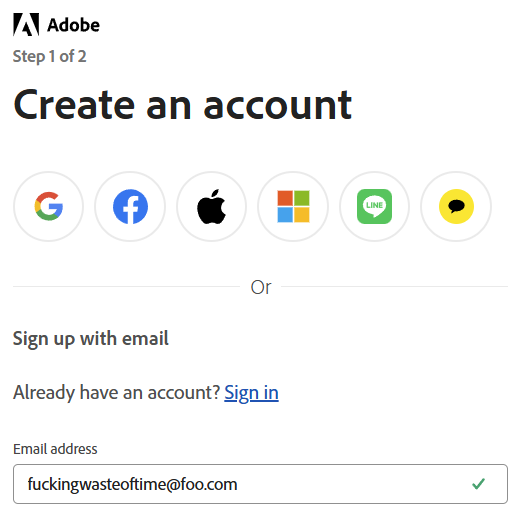
Any questions, Bruce? That is simply as simply explainable as why we thought-about it a sound handle and ingested it into HIBP: the e-mail handle has a sound construction. That’s all. That is the way it received into Adobe, and that is the way it then flowed by way of into HIBP.
Ah, however should not Adobe confirm the handle? I imply, should not they ship an e-mail to the handle alongside the traces of “Hey, are you positive you need to enroll in this service?” Sure, they need to, however this is the kicker: that does not cease the e-mail handle from being added to their database within the first place! The way in which this usually works (and that is what we do with HIBP if you join the free notification service) is you enter the e-mail handle, the system generates a random token, after which the 2 are saved collectively within the database. A hyperlink with the token is then emailed to the handle and used to confirm the person in the event that they then observe that hyperlink. And if they do not observe that hyperlink? We delete the e-mail handle if it hasn’t been verified inside a couple of days, however evidently, Adobe does not. Most companies do not, so right here we’re.
How Can I Be Actually Certain Precise Pretend Addresses Aren’t in HIBP?
That is additionally going to look profoundly apparent, however genuinely random e-mail addresses (not “thisisfuckinguseless@”) will not present up in HIBP. Need to take a look at the speculation? Strive 1Password’s generator (sure, Bruce, additionally they sponsor HIBP):
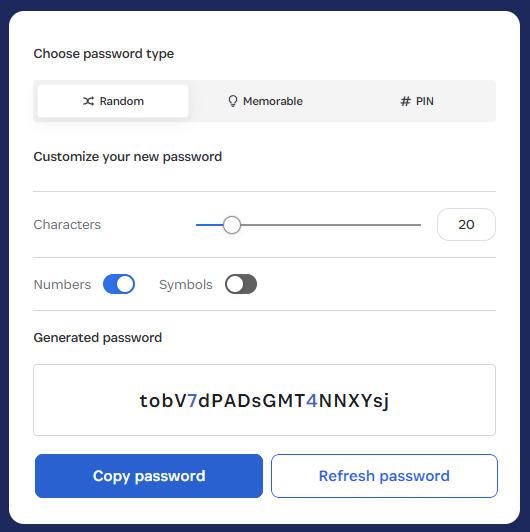
Now, whack that on the foo.com area and do a search:
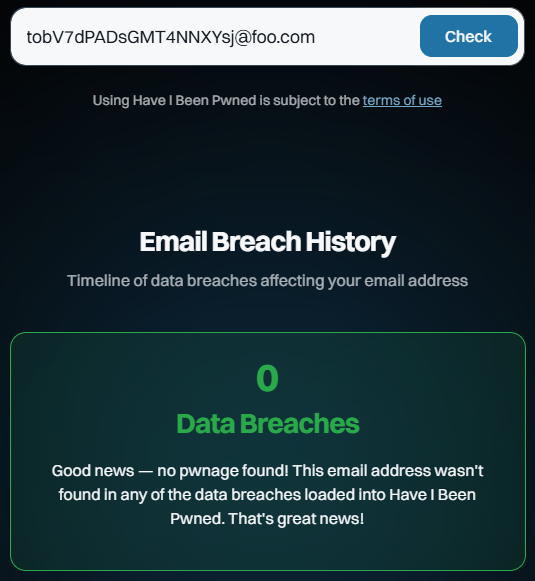
Huh, would you take a look at that? And you’ll preserve doing that over and over. You’ll get the identical consequence as a result of they’re fabricated addresses that nobody else has created or entered into an internet site that was subsequently breached, ipso facto proving they can not seem within the dataset.
Conclusion
Right this moment is HIBP’s twelfth birthday, and I’ve taken explicit problem with Bruce’s assessment as a result of it calls into query the integrity with which I run this service. That is now the 218th weblog publish I’ve written about HIBP, and over the past dozen years, I’ve detailed every little thing from the structure to the moral concerns to how I confirm breaches. It is onerous to think about being any extra clear about how this service runs, and per the above, it is very easy to disprove the Bruces of the world. If you happen to’ve learn this far and have an correct, fact-based assessment you want to go away, that’d be superior 😊



